One way to ensure that your visitors access to your website via secure connection is to redirect HTTP requests to HTTPS by using IIS URL Rewrite module. You will find step-by-step instructions to configure IIS in this post.
Note that you may need to spend some extra effort on configuration if you have a load balancer that hosts SSL certificates (SSL offloading). Please check the last section (“If your web server is behind a Load Balancer…”) at the end of this post for more information.
Looking for an alternative way to redirect HTTP requests to HTTPS? Check this post out.
Redirect HTTP requests to HTTPS by using IIS URL Rewrite
Follow the steps below to redirect all HTTP requests to your HTTPS URL.
- Download and install URL Rewrite module
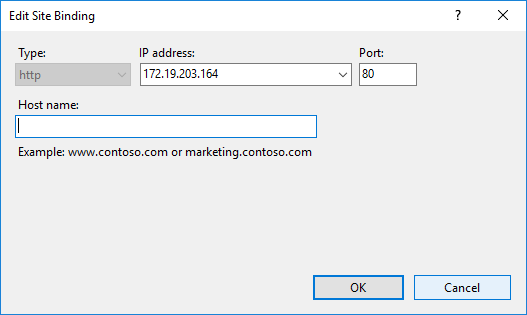
- Make sure that your website is accessible via HTTP (Check Site Binding to make sure there is a binding for port 80)
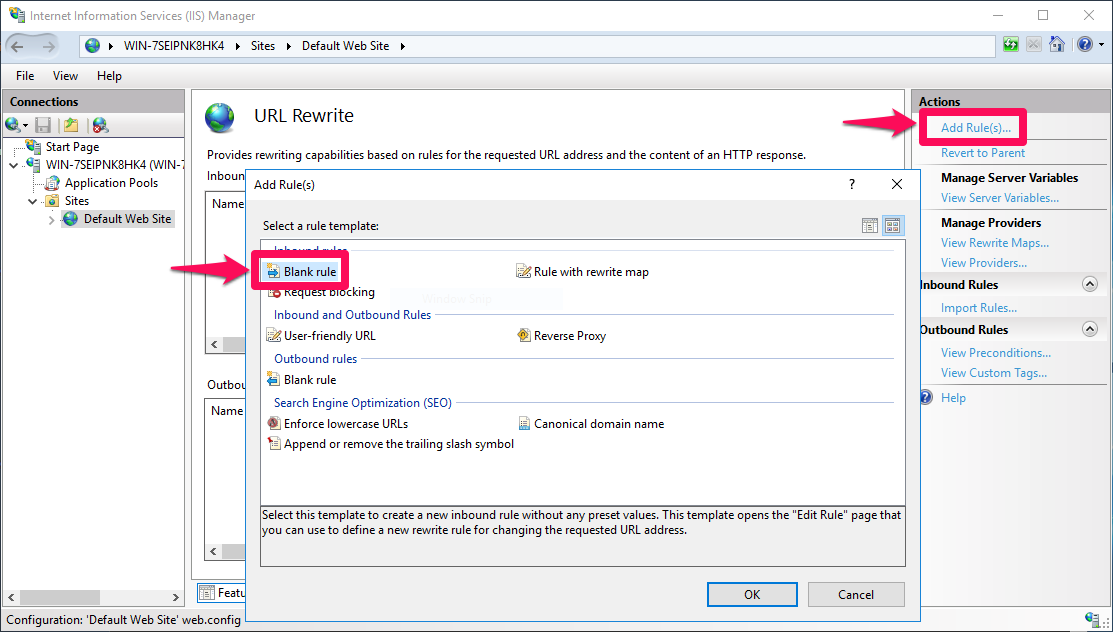
- In server, site or application level, go to URL Rewrite feature
- Click “Add Rule(s)” in the “Actions” pane
- Select “Blank rule“. Click “OK“
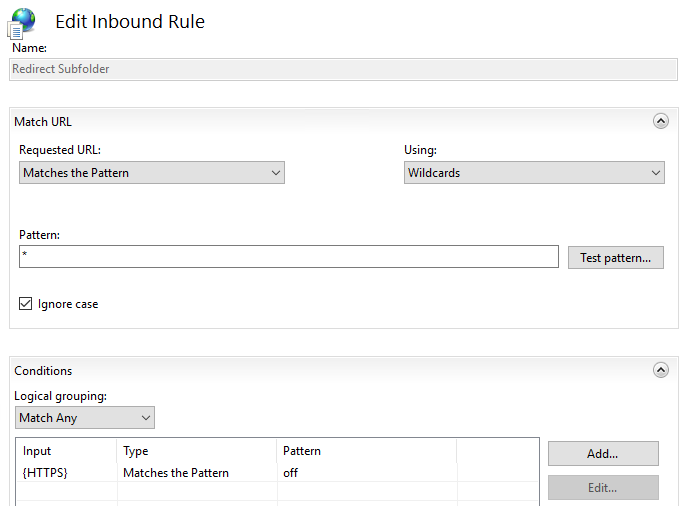
- Select “Matches the Pattern” from “Requested URL” menu
- Select “Wildcards” from “Using” menu
- Enter
*into “Pattern” field - Add a new condition with input
{HTTPS}, type “Matches the Pattern“, patternoff. This condition will make sure to prevent indefinite loop from HTTPS to HTTPS. The condition will make sure the rule is executed if the request is not HTTPS
- In the “Action” section, select “Redirect” from “Action type” menu
- Enter
https://{HTTP_HOST}{REQUEST_URI}into “Redirect URL” field. Click here for more information about server variables and URL parts
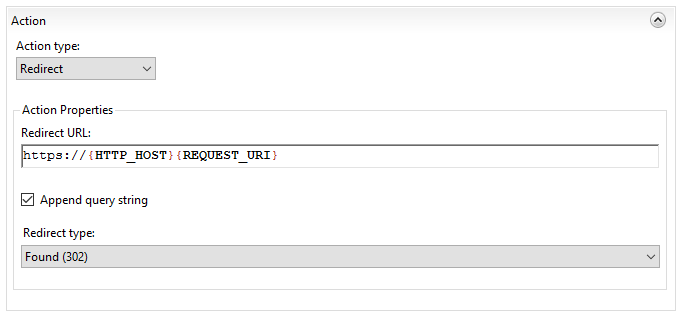
- Click “Apply” in the “Actions” pane
- Try to access your site/application via HTTP URL and check if it is redirected to HTTPS
Web.config changes
When you add, edit or remove a URL Rewrite URL, corresponding web.config file is automatically updated. Go to application folder and open the web.config file if you want to view the changes.
<rewrite>
<rules>
<rule name="Redirect Subfolder" enabled="true" patternSyntax="Wildcard" stopProcessing="true">
<match url="*" ignoreCase="true" />
<conditions logicalGrouping="MatchAny">
<add input="{HTTPS}" pattern="off" />
</conditions>
<action type="Redirect" url="https://{HTTP_HOST}{REQUEST_URI}" redirectType="Found" />
</rule>
</rules>
</rewrite>Not working? Try these
If the URL Rewrite rule for redirection is not working (HTTP requests continue to go to HTTP site), I would recommend using Failed Request Tracing (FRT) to troubleshoot redirection. Here is a link for instructions to use FRT for URL Rewrite troubleshooting.
Additionally, try the recommendations below to solve the issue:
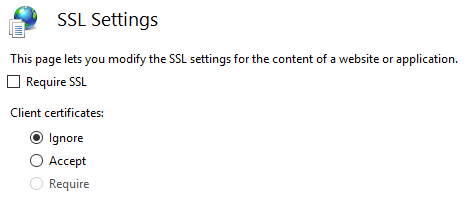
- Make sure that “Require SSL” is unchecked in “SSL Settings”
- Instead of a wildcard, try using a regex in “Match URL” section (Select “Regular Expressions” from “Using” list. Enter
(.*)into “Pattern” field). More information - Try
^OFF$pattern for the condition. More information
- Previous URL Rewrite rule might have cached. Try to use server variable from this list that disable kernel mode caching for all requests. You can also try disabling internal cache of rewritten URLs. Here is a list of registry values for IIS URL Rewrite.
If your web server is behind a Load Balancer…
Many companies leverage load balancers to distribute workload among several web servers. If this is the case in your environment, you may need to change the server variable you use in the condition of your URL Rewrite rule.
In the instructions above, we used {HTTPS} header to check the usage of HTTPS protocol. The load balancer in your network may remove this header from requests. A better practice in this scenario is to use {HTTP_X_FORWARDED_PROTO} header. Click here for more information.
Here is the web.config entry for an example URL Rewrite rule using {HTTP_X_FORWARDED_PROTO} header:
<rewrite>
<rules>
<rule name="HTTPS Redirect" stopProcessing="true">
<match url="(.*)" />
<conditions>
<add input="{HTTP_X_FORWARDED_PROTO}" pattern="https" negate="true" />
</conditions>
<action type="Redirect" url="https://{HTTP_HOST}/{R:1}" />
</rule>
</rules>
</rewrite>
2 thoughts on “How to redirect HTTP requests to HTTPS by using IIS URL Rewrite”